Top 7 Responsibilities of a Breach Response Team

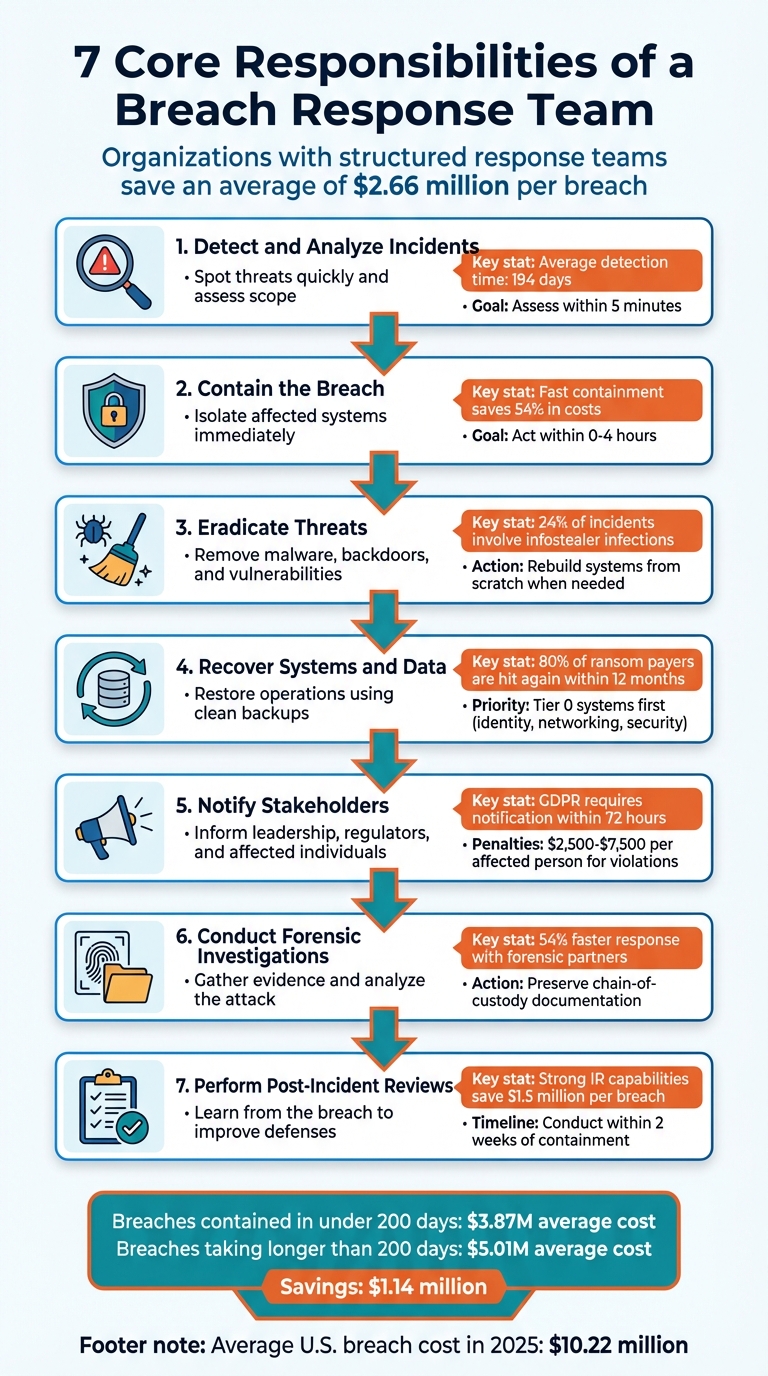
When a data breach strikes, the clock starts ticking. Companies with a dedicated breach response team can dramatically reduce the financial and operational impact of such incidents. Without one, the average cost of a U.S. breach in 2025 hit $10.22 million, while organizations with structured response teams saved an average of $2.66 million per breach.
Here are the 7 core responsibilities of a breach response team:
- Detect and Analyze Incidents: Spot threats quickly, assess their scope, and document key details.
- Contain the Breach: Isolate affected systems to prevent further damage.
- Eradicate Threats: Remove malware, backdoors, and vulnerabilities to stop future attacks.
- Recover Systems and Data: Restore operations securely using clean backups.
- Notify Stakeholders: Inform leadership, regulators, and affected individuals within required timelines.
- Conduct Forensic Investigations: Gather evidence, analyze the attack, and create a timeline.
- Perform Post-Incident Reviews: Learn from the breach to improve future response efforts.
Companies with fast response times - under 200 days - save millions and limit reputational damage. These responsibilities ensure swift action, compliance, and long-term security improvements.
7 Core Responsibilities of a Breach Response Team
Breach Mode: Real-World Incident Response Playbooks and Lessons
sbb-itb-e766981
1. Detect and Analyze Incidents
The first step in defending against cyber threats is recognizing the warning signs before a minor issue spirals into a full-blown crisis. Breach response teams focus on spotting network anomalies, unusual traffic patterns, and unauthorized access attempts across both on-premises and cloud systems [3][6]. For instance, when critical systems unexpectedly go offline, it could indicate an active ransomware attack [7]. Once an issue is detected, a swift and structured analysis is essential to prevent further damage.
Modern detection relies heavily on automated alerts from tools like SIEM, EDR, and IDS/IPS systems [6][8]. These tools help teams quickly decide if an alert is a false alarm or a genuine threat - ideally within five minutes [8]. A stark reminder of the importance of rapid detection is the September 2025 attack on National Presto Industries by the InterLock ransomware group. The attackers breached the company and its subsidiaries, including National Defense Corporation and AMTEC, and leaked nearly three million files. This highlights how delays in detection can lead to devastating consequences [6].
Once a breach is identified, teams work to assess its scope, impact, and severity. This involves documenting all indicators of compromise (IoCs) with precise timestamps, determining if the attack is ongoing, and identifying the type of data exposed - whether it’s personal information, financial records, or login credentials [3][5]. By retracing the attacker’s movements, from initial entry to lateral spread, teams can piece together a complete timeline of the incident [5]. Organizations that detect and contain breaches within 200 days save an average of $1.1 million compared to those that take longer [5].
During the analysis phase, preserving evidence is just as important as acting fast. Teams must secure volatile data, such as memory dumps and forensic disk images, and complete a thorough scope assessment within 30 minutes [3][5][8]. Logs from systems, applications, firewalls, and authentication sources are also collected and moved to secure locations to prevent overwriting [3].
Speed is everything in this process. The average time to detect a breach in 2025 was 194 days - a sobering statistic [8]. To streamline responses, teams assign severity levels to incidents. For example, a SEV-1 (Critical) event, like an active data theft, demands action in under 15 minutes. Meanwhile, a SEV-4 (Low) event, such as a minor policy violation, can be addressed within 24 hours [8]. Effective detection and analysis lay the groundwork for the rapid containment and recovery steps that follow.
2. Contain the Breach
When a breach is confirmed, swift action is crucial to limit the damage. Start by disconnecting compromised systems - unplug network cables or disable adapters instead of shutting them down. This preserves volatile memory, which can be critical for investigations [3][5]. Cutting off access immediately helps prevent attackers from moving laterally to other servers or workstations.
Once systems are isolated, the next priority is securing access credentials. Disable compromised accounts, block suspicious IP addresses, and revoke access rights. However, timing is everything. As Sarah Chen, Senior Cybersecurity Engineer at ZeonEdge, advises:
"If you detect an active intrusion, don't change the compromised user's password immediately - the attacker will know they've been detected and may accelerate data exfiltration or deploy destructive payloads" [11].
Instead of rushing to change passwords, focus on isolating the network path first. Once the attacker is cut off, you can safely revoke access without tipping them off prematurely.
Segmenting the network is another key step to limit the breach's scope. Rather than shutting down the entire infrastructure, isolate the attack to specific VLANs or adjust compromised applications behind Web Application Firewall (WAF) rules [5][11]. Additionally, halt all active data transfers and block known Command and Control (C2) domains at the firewall level [9][11].
Communication during this phase is critical - and attackers may be monitoring internal systems. Use encrypted, external communication tools to ensure your response team can coordinate without being observed [2][5].
Fast containment doesn’t just protect systems; it also saves money. Companies that contain breaches quickly can cut costs significantly - by as much as 54% [1]. Breaches resolved in under 200 days cost $1.26 million less, on average, than those that take longer [9]. That’s why experts emphasize acting within the first 0–4 hours of discovery [3]. Stéphane Nappo, Global Head of Information Security at Société Générale, captures the stakes perfectly:
"It takes 20 years to build a reputation and a few minutes of cyber-incident to ruin it" [9].
3. Eradicate Threats
Once containment is achieved, the next essential step is to completely eliminate the threat to prevent it from resurfacing. While containment limits the immediate damage, eradication ensures the root cause - whether it's malware, backdoors, or exploited vulnerabilities - is permanently removed. As Josh Amishav from Breachsense points out:
"Traditional malware incident response is broken. Most playbooks focus on one thing: cleaning infected devices. That made sense a decade ago. Today, it's a recipe for getting breached again within weeks" [12].
Modern threats demand more advanced strategies than just running antivirus software. For example, infostealer infections - responsible for 24% of all security incidents in 2024 - require teams to invalidate active session tokens and browser cookies [12]. This is critical because attackers can exploit stolen session data to bypass multi-factor authentication, even after passwords are reset. To fully secure credentials, cleanup must be performed from devices that are confirmed to be safe and uninfected. This approach ensures attackers can’t leverage any lingering session data, paving the way for complete system recovery.
For assets that are severely compromised, rebuilding systems from scratch is often the best course of action. Trying to clean infected systems can leave behind hidden persistence mechanisms, while a full rebuild guarantees their removal. Before starting the rebuild process, it’s crucial to preserve forensic evidence for further analysis. Once the systems are restored, patch any vulnerabilities that were exploited, whether it’s outdated software, misconfigurations, or open ports. If these vulnerabilities remain unaddressed, attackers could easily strike again. Fixing these issues during eradication not only prevents repeat breaches but also strengthens the organization’s overall security posture.
The eradication process doesn’t stop at endpoints. For cloud-related breaches, it’s essential to review container images and serverless functions for any injected code. Additionally, rotate all API keys and service account credentials to block potential access points. When restoring systems from backups, always scan the backups in an isolated environment to ensure the threat isn’t reintroduced. Interestingly, organizations using AI-driven security tools have managed to reduce their breach lifecycle from 241 days to less than 200 days [13], showing how automation can significantly speed up the eradication process.
To wrap up eradication efforts, conduct thorough threat-hunting activities to identify any remaining indicators of compromise (IoCs) and monitor for potential secondary attacks. The ultimate goal is not just removing what’s visible but ensuring no hidden threats remain to cause future harm.
4. Recover Systems and Data
Once threats have been eliminated, the next step is to restore operations. However, recovery isn’t just about getting systems back online - it’s about creating a clean, secure environment that ensures the same threat won’t resurface.
Start by locating your "last known good" backup, which is the backup taken before the earliest confirmed compromise. If you can’t confidently identify a safe restore point, treat the incident as a potential integrity breach and revert to an earlier backup. From there, prioritize what to recover based on how critical the systems are to your business:
- Tier 0 systems: These include identity platforms like Active Directory, core networking, backup infrastructure, and security tools. These should be restored first.
- Tier 1 systems: Customer-facing and revenue-generating applications come next.
- Tier 2 systems: Internal applications follow.
- Tier 3 systems: Finally, recover endpoints.
The goal of recovery is to build a secure, operational environment that complements the eradication efforts. This involves rebuilding infrastructure with hardened baselines and patched operating systems to remove any lingering persistence mechanisms. Before reconnecting any system to production, take these critical steps:
- Scan restored datasets for malware.
- Perform checksum validations.
- Conduct database consistency checks.
- Rotate all credentials immediately.
Once systems are operational, keep a close eye on them. For the next 14–30 days, enable intensive monitoring, increase logging levels, and deploy Endpoint Detection and Response (EDR) tools on clean systems before reintroducing application data.
Here’s a sobering statistic: 80% of organizations that pay a ransom are hit again within 12 months [13]. This underscores the importance of a thorough recovery process. Cutting corners can leave your organization vulnerable to repeat attacks. By combining a meticulous recovery strategy with the security improvements made during threat eradication, you’ll create a stronger, more resilient environment.
5. Notify Stakeholders
After containing the breach and initiating recovery, it’s time to communicate the incident. How, when, and who you notify can determine whether the situation remains manageable or spirals into a legal disaster. Missing notification deadlines can lead to hefty fines and damage to your reputation. Quick and accurate communication is a cornerstone of any breach response plan.
Start by notifying internal leadership - such as the CEO, CISO, CTO, General Counsel, and Board members - within the first 0–4 hours [3][4]. These individuals will approve necessary resources, make key decisions, and prepare for potential fallout. Simultaneously, involve legal counsel to establish attorney-client privilege over the investigation and to navigate regulatory obligations [3][1].
Regulatory notifications are a top priority. Under GDPR, you must notify supervisory authorities within 72 hours of discovering the breach [3]. HIPAA allows up to 60 days, but breaches affecting more than 500 individuals require immediate notification to the Department of Health and Human Services [3]. California’s CCPA mandates notification "without unreasonable delay" [3]. Missing these deadlines can result in penalties ranging from $2,500 to $7,500 per affected person [16]. Once regulatory bodies are informed, attention should shift to notifying affected individuals.
When contacting customers, confirm the scope of compromised data first. Many states require notification within 30 to 60 days, while 31 states use less specific guidelines like "without unreasonable delay" [15]. To save time, prepare notification templates in advance, so they can be quickly tailored to the situation [2][5]. Additionally, set up a toll-free hotline for inquiries and offer at least 12 months of free credit monitoring - this is mandatory in six states and widely considered best practice elsewhere [15][16].
During an active breach, use out-of-band, encrypted communication channels to coordinate your response. If corporate email or messaging systems are compromised, attackers might be monitoring your efforts [2][5]. Keep detailed records of all notifications, including timestamps and content, for regulatory and legal purposes [3][14]. As Ann Snook from Case IQ emphasizes:
"The speed, accuracy, and coordination of your response can significantly impact legal exposure, financial loss, and reputational damage" [14].
Once stakeholders are notified, your team can focus on the next steps in the recovery process.
6. Conduct Forensic Investigations
Once stakeholders are notified, the next step is to secure and analyze evidence to understand how attackers gained access, what actions they took, and which data might have been compromised. This process creates a detailed record that can withstand audits, regulatory checks, and even legal challenges.
Start by preserving all evidence. Capture forensic images and calculate SHA-256 hashes to ensure data integrity before initiating any cleanup. Keep affected systems powered on but disconnected from the network. Shutting them down erases volatile memory (RAM), which often holds critical details like running processes or encryption keys. As Pentest Testing notes:
"Modern incidents don't fail because security teams lack tools - they fail because the evidence wasn't collected, preserved, or correlated in a way that survives audits, regulators, insurance reviews, or legal scrutiny."
Focus on gathering evidence from essential sources, such as web applications, APIs, cloud environments, CI/CD pipelines, and identity systems. Every piece of evidence requires a strict chain-of-custody record, documenting who collected it, the exact time (in UTC), and its storage location. Use immutable or WORM (Write Once Read Many) storage to safeguard this data from tampering, and ensure log retention policies are frozen to prevent overwriting critical information.
Once the evidence is secured, reconstruct the attack timeline. This involves correlating logs using unique identifiers, analyzing malware in secure sandboxes, capturing network traffic with tools like Wireshark, and using memory forensics platforms such as Volatility to examine RAM dumps. Conduct a root cause analysis to identify entry points and assess the extent of data exposure.
Organizations with incident response plans and external forensic partners can cut response times by 54% [3]. A thorough forensic investigation does more than explain what happened - it provides legal-grade documentation to satisfy regulators, support insurance claims, and even aid in prosecuting attackers. These findings are invaluable for post-incident reviews, helping to refine security measures and improve the organization's overall breach response process.
7. Perform Post-Incident Reviews
Hold a post-incident review within two weeks of containing the breach to capture fresh insights while the details are still clear [3]. The goal? Understand what went right, what went wrong, and how to stop similar attacks in the future.
Bring together all key teams - IT, security, legal, HR, and communications - and build a detailed, minute-by-minute timeline of the breach [2][3]. Dive deep with a root cause analysis to uncover the technical, procedural, or human errors that allowed the breach to happen [3][14].
Evaluate how well your team responded by analyzing communication flows, identifying technology gaps, and pinpointing decision-making delays. Here’s why this matters: Organizations with strong incident response capabilities save an average of $1.5 million per breach compared to those without them [6]. Use these insights to improve your incident response plan, refine playbooks, and add preventive measures like multi-factor authentication or better logging systems [2][14]. These adjustments are your roadmap to a stronger defense.
As Secure.com puts it:
"Post-incident reviews aren't optional - they're where your team learns to prevent the next attack" [7].
Track your progress using metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) [6]. Once your plan is updated, test it immediately through tabletop exercises or simulations [2][1]. Even small incidents deserve a review - they often expose vulnerabilities that could lead to much bigger problems [7]. Completing these updates reinforces your response strategy.
Don’t forget to store your updated response plan and emergency contacts externally to ensure you can access them during future incidents. With the average cost of a U.S. data breach now reaching $10.22 million [7], these reviews are a critical investment in protecting your organization from future attacks.
Conclusion
A breach response team’s responsibilities - spanning from detecting incidents to performing post-incident reviews - work together to limit damage and speed up recovery efforts. These roles include detecting threats, containing them, eradicating issues, restoring systems and data, notifying stakeholders, conducting forensic investigations, and reviewing incidents afterward. Together, they create a cohesive defense strategy that’s both proactive and responsive.
The financial advantages of a well-prepared team are hard to ignore, often requiring the strategic oversight of fractional CFO services. A structured and tested response plan can save organizations millions during a breach [1][3]. For instance, breaches identified and managed within 200 days cost an average of $3.87 million, compared to $5.01 million for those with slower responses - a difference of $1.14 million [17][5]. This underscores how preparation can directly impact the bottom line.
Clear role definitions ensure that technical, legal, and communication efforts happen simultaneously rather than in a drawn-out sequence. Using a RACI matrix (Responsible, Accountable, Consulted, Informed), key players like the Incident Commander, IT Lead, Legal Counsel, and Communications Lead know their exact responsibilities during a crisis [1]. This coordination significantly reduces response and recovery times [6][10].
To move from reactive to proactive crisis management, regular practice and updated resources are essential. Conduct quarterly tabletop exercises to test your team’s ability to make decisions under stress [1][14]. Keep offline contact lists and playbooks ready in case your network becomes inaccessible [1]. Additionally, consider a hybrid approach - using internal staff for immediate actions while retaining external forensic experts for specialized tasks [1]. These measures ensure your organization is ready to handle breaches with confidence and efficiency.
FAQs
Who should be on a breach response team?
A well-prepared breach response team is essential for managing crises effectively. It should include key roles like an incident commander - typically a senior executive who oversees the response, an IT/security lead to address technical issues, legal counsel to handle compliance and liability matters, and communications personnel to manage internal and external messaging. Assigning these responsibilities ahead of time ensures everyone knows their role, enabling quicker and more coordinated decision-making when a breach occurs.
What should we do in the first hour after discovering a breach?
During the first hour, prioritize containing the breach by isolating any affected systems. Avoid deleting files or shutting systems down, as this could compromise valuable evidence. At the same time, activate your incident response team to coordinate efforts and ensure every action is documented with precise timestamps. These steps are essential for limiting damage and preserving a detailed record for further investigation.
How do we know which backups are safe to restore after a breach?
To make sure backups are safe to use after a breach, they need to go through a careful verification process. This includes checking that they’re free of malware and confirming their integrity with forensic analysis. These steps ensure the backups are secure and reliable for restoration.




