Top 7 Third-Party Risk Management Practices

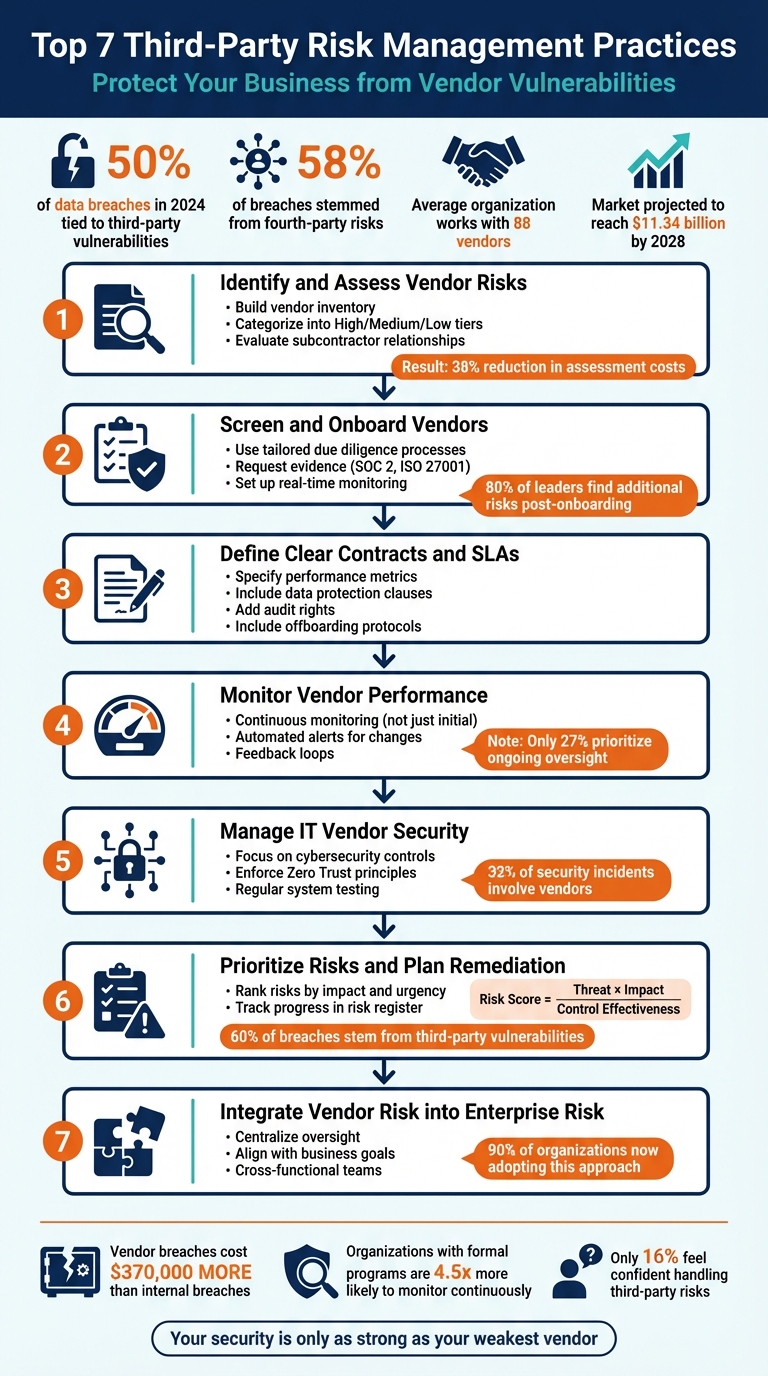
Your vendors can be your weakest link - or your strongest safeguard. Nearly 50% of data breaches in 2024 were tied to third-party vulnerabilities, and 58% of these breaches stemmed from fourth-party risks. The stakes? Financial losses, reputational damage, and operational disruptions. Managing these risks isn’t optional - it’s a necessity.
Here’s how to protect your business with seven key practices:
- Identify and Assess Vendor Risks: Build a vendor inventory, categorize risks into tiers, and evaluate subcontractor relationships.
- Screen and Onboard Vendors: Use tailored due diligence processes, request evidence (e.g., SOC 2 reports), and set up real-time monitoring.
- Define Clear Contracts and SLAs: Specify performance metrics, data protection clauses, and audit rights. Include offboarding protocols.
- Monitor Vendor Performance: Go beyond initial due diligence with continuous monitoring, automated alerts, and feedback loops.
- Manage IT Vendor Security: Focus on cybersecurity controls, enforce Zero Trust principles, and regularly test vendor systems.
- Prioritize Risks and Plan Remediation: Rank risks by impact and urgency, then track progress in a risk register.
- Integrate Vendor Risk into Enterprise Risk: Centralize oversight, align risks with business goals, and involve cross-functional teams.
These steps ensure vendors meet your security, compliance, and operational standards throughout their lifecycle. With businesses relying on an average of 88 vendors - and the third-party risk management market projected to reach $11.34 billion by 2028 - this approach is more important than ever.
7 Essential Third-Party Risk Management Practices for Business Security
1. Identify and Assess Vendor Risks
Risk Identification and Categorization
Start by creating a detailed inventory of all vendors, including those operating under the radar as "shadow IT." This list should capture each vendor’s services, the data they access, and their internal points of contact [5][8]. With organizations working with an average of 88 third-party vendors [8], this inventory becomes the backbone of your risk management strategy.
Not all vendors require the same level of scrutiny. For example, a plumbing service doesn't need the same rigorous assessment as a cloud provider managing sensitive customer data [2]. To streamline the process, categorize vendors into High, Medium, and Low risk tiers based on criteria like access to sensitive data (e.g., PII or PHI), network access, and their role in business continuity [6][5][3]. This tiered approach not only improves focus on critical vendors but also helps cut costs - organizations using this method report a 38% reduction in assessment costs and a 27% increase in coverage for critical vendors [5].
| Vendor Tier | Risk Level | Characteristics | Assessment Depth |
|---|---|---|---|
| Tier 1 | High | Handles sensitive data (PII/PHI), vital for operations, integrates with networks. | Comprehensive due diligence, onsite audits, continuous monitoring. |
| Tier 2 | Medium | Moderate data access, important but not critical role. | Standardized questionnaires, periodic reviews. |
| Tier 3 | Low | Limited data access, minimal operational impact (e.g., office supplies). | Basic compliance checks, streamlined assessments. |
Before applying any security measures, assess the inherent risk each vendor poses [2]. Then, dig deeper into specific risk factors across key areas like cybersecurity (e.g., data breaches), financial stability, compliance (e.g., regulatory fines), and even ESG (environmental, social, and governance) concerns [7][2]. This evaluation also needs to extend to subcontractors and fourth-party relationships, which account for 58% of third-party breaches [5].
Don’t take vendors’ security claims at face value - especially if they rely on cloud hosting platforms like AWS or Azure. Jeff Hudgens from HBS emphasizes:
"Your security is only as strong as your weakest vendor" [3].
Cloud hosting doesn’t protect against a vendor’s internal misconfigurations or poor access controls [3]. Always verify their claims with solid evidence, such as third-party audit reports like SOC 2 Type II, ISO 27001, or HITRUST certifications, instead of relying on self-reported assurances [3][4].
This thorough risk identification process lays the groundwork for effective vendor screening and onboarding in the next phase of your strategy.
sbb-itb-e766981
2. Screen and Onboard Third-Party Vendors
Vendor Screening and Documentation
Once you've identified potential vendors, the next step is a thorough screening and onboarding process. This starts with automated checks against sanctions lists, Politically Exposed Persons (PEP) databases, and adverse media sources to flag immediate concerns [9]. Beyond these initial checks, due diligence involves a deeper dive, including detailed security questionnaires, document reviews, and audits tailored to the vendor's specific risk profile [9].
The level of documentation you require should match the vendor's risk level. For high-risk vendors, such as those handling sensitive data, request comprehensive evidence like SOC 2 Type II reports, ISO 27001 certifications, recent penetration tests, Business Continuity Plans, and proof of cyber insurance [12]. For vendors with lower risk, like office supply providers, simpler checks - such as sanctions screening and credit evaluations - are usually enough [12]. This tailored approach ensures resources are allocated where they matter most.
Avoid relying on yes/no questionnaires. Instead, ask for detailed evidence, such as policy documents or audit reports. As Deqian Jia, Founder at Peony, puts it:
"You are never 'just' buying software or a service. You're buying a slice of someone else's operational, security, and compliance reality - and welding it onto your own" [12].
If a vendor claims their security is robust because they use AWS or Azure, dig deeper. Review their own configurations, access controls, and encryption practices rather than relying solely on the cloud provider's SOC 2 report [3].
After completing the screening, continue the process with ongoing monitoring to ensure risks remain under control.
Monitoring and Continuous Improvement
Vendor onboarding doesn’t end once the contract is signed. In fact, over 80% of legal and compliance leaders report uncovering additional risks after onboarding [9]. To stay ahead, set up automated alerts for any changes in a vendor's credit score, cyber risk rating, or mentions in adverse media [9]. This kind of real-time monitoring helps maintain a strong risk management framework.
Limit vendors’ access to your systems by enforcing least privilege principles, requiring multi-factor authentication, and setting expiration dates for credentials [10]. Continuous oversight ensures that even after onboarding, risks are managed effectively.
Kezia Farnham, Senior Manager at Diligent, highlights the importance of this process:
"It's not uncommon to find an issue when onboarding vendors (in fact, if you never find a single issue, that in itself is a risk!)" [11].
If your screening process uncovers vulnerabilities - like weak encryption or outdated controls - address these before finalizing the contract [10]. And don’t forget to plan for the end of the relationship. Use an offboarding checklist to revoke access and secure your data when the partnership concludes [10].
3. Create Clear Contracts and Service Level Agreements
Contractual Clarity and Compliance
A well-defined contract is the cornerstone of any successful vendor partnership. It’s essential to clearly outline the scope of services to avoid "scope creep", where vendors gradually take on responsibilities or access beyond the original agreement [2][13]. Incorporate specific performance metrics into your Service Level Agreements (SLAs). These should include measurable benchmarks like uptime requirements, response times, and delivery schedules. To ensure accountability, tie these metrics to penalties or service credits in cases of non-compliance [13][14][15].
Data protection is another critical component. Contracts should include clauses that detail how data will be handled, stored, and encrypted, along with strict timelines for breach notifications [6]. If your organization is governed by regulations like GDPR or HIPAA, the contract should mandate vendor compliance, supported by certifications such as SOC 2 or ISO 27001 [3][6][15]. Avoid relying on generic vendor templates - customize terms to reflect your organization’s risk tolerance and strategic objectives [13][14]. To enforce these agreements, include provisions for measurable audit rights.
A "right to audit" clause is particularly important. This allows you to verify the vendor’s security practices through periodic assessments or third-party reports [13][6][15]. This step is crucial given that nearly 30% of data breaches now involve third parties [15].
Additionally, require vendors to disclose their subcontractor relationships and ensure that your security standards extend to these fourth-party vendors [6][15]. With the Business Process Outsourcing market expected to hit $525 billion by 2030 [14], these hidden dependencies pose growing risks.
Contracts should also address offboarding procedures. Specify how data will be returned or securely destroyed at the end of the relationship [2][13]. This is vital, as 39% of companies fail to manage third-party risks effectively during offboarding [2]. By documenting clear exit protocols, you can mitigate lingering vulnerabilities. As the Auditive Team aptly puts it:
"A managed contract is not a static document, it's a tool for continuous collaboration." [13]
From setting performance expectations to planning for the end of the relationship, well-crafted contracts strengthen your risk management framework. At Phoenix Strategy Group, we focus on tailoring contracts to an organization’s specific risk profile, ensuring that every vendor relationship is built on transparency and accountability.
4. Monitor Vendor Performance and Compliance
Monitoring and Continuous Improvement
Once you've screened vendors and outlined clear contracts, the real work begins - keeping a close watch on vendor performance and compliance over time. Surprisingly, many organizations fall short here. While 73% of efforts focus on initial due diligence, only 27% prioritize ongoing oversight [8]. This gap can leave businesses exposed to new risks that emerge after a vendor relationship is established. For instance, 66% of companies report data breaches caused by vendor failures, yet only 34% trust vendors to report breaches in a timely manner [7].
To stay ahead of these risks, effective monitoring requires more than an annual checklist - it demands real-time visibility. Companies with formal cyber risk programs are 4.5 times more likely to continuously monitor their vendor relationships [4]. This involves setting up automated alerts for critical changes, such as dips in security ratings, financial instability, or compliance issues [8]. Tools like Google Alerts can be invaluable - track vendor names alongside terms like "lawsuit", "data breach", or "bankruptcy" to catch potential red flags early [16][17]. For public vendors, quarterly filings can reveal financial health, while private vendors should provide audited financial statements or similar documentation [16].
The level of monitoring should align with the vendor's risk profile. Vendors handling sensitive data or playing a key role in business operations require more frequent reviews - ideally annually. Lower-risk vendors, on the other hand, may only need reassessments every two to three years [16]. Don’t assume that using major platforms like AWS or Azure guarantees security; vendor configurations and controls must still be verified [3]. As Jeff Hudgens from Harvard Business School aptly notes:
"Your security is only as strong as your weakest vendor" [3].
Engaging operational teams that work directly with vendors can also provide valuable insights. These teams are often the first to notice performance issues, so their feedback is essential [16][17]. Metrics to monitor should cover multiple areas, such as:
- Cybersecurity: Ransomware exposure, vulnerability management
- Financial Health: Credit ratings, workforce changes like layoffs
- Operational Performance: SLA adherence, response times
- Compliance: Consumer complaints, pending legal actions in databases like the CFPB [16][17]
Modern AI tools can streamline this process, cutting assessment times by up to 75% by automatically mapping vendor documentation to standards like NIST or ISO 27001 [4].
At Phoenix Strategy Group, we specialize in helping growth-stage companies build scalable monitoring frameworks. By combining automated alerts with strategic oversight, you can shift from reacting to problems to proactively managing risks. This ensures that your vendors consistently meet your security and business standards throughout the partnership, seamlessly integrating into your broader risk management approach.
5. Manage IT Vendor Security Risks
Risk Identification and Categorization
Managing IT vendor security requires a focused, tailored approach. Third-party relationships are a major source of security challenges, with 33% of security incidents involving vendors and an average breach costing $4.91 million [6][18]. Between 2023 and 2024, 80% of organizations reported experiencing a supply-chain attack, underscoring the growing threat landscape [18].
Start by assessing each vendor's inherent risk score before implementing security controls [2]. Vendors should be categorized into tiers - low, medium, high, or critical - based on factors like the sensitivity of data they handle (e.g., PII, PHI), their role in your operations, regulatory compliance needs, and their network access level [6][2][3]. For IT vendors, it's crucial to also evaluate their subcontractors to understand potential dependencies [6][2].
The rise of AI integrations has added new challenges, such as concerns about data lineage, model transparency, and automated decision-making. Notably, 30% of AI-related security incidents stem from third-party SaaS vendors [18].
Vendor Screening and Documentation
Screening vendors effectively means going beyond surface-level checks. Look for issues like unpatched software, misconfigurations, weak APIs, or leaked credentials. Use recognized frameworks such as SOC 2, ISO 27001, NIST CSF, and HITRUST to validate a vendor's security practices, but don't rely solely on their self-reported compliance [6][18][4]. Request third-party audit reports and penetration test results to verify their claims [3][4].
Even if a vendor uses cloud services like AWS or Azure, it’s essential to confirm their internal configurations and controls. A cloud provider’s certifications don’t automatically extend to the vendor’s practices [3]. These technical checks lay the groundwork for clear and enforceable security contracts.
Contractual Clarity and Compliance
Contracts with IT vendors should explicitly define security responsibilities. This includes requirements like 24-hour incident reporting, audit rights, and detailed data handling protocols [6][7]. Service Level Agreements (SLAs) should also specify uptime expectations and recovery time objectives (RTO) that reflect your organization’s risk tolerance [18][7].
With the increasing use of AI, modern contracts now often require vendors to disclose whether they use AI and if customer data will be used for training models [6]. For example, Twilio’s 2022 security breach - caused by a social engineering attack exploiting weak vendor controls - highlighted the importance of including enforcement mechanisms in contracts. These can include financial penalties, service credits, or termination rights for vendors that fail to meet security standards [6][18].
Monitoring and Continuous Improvement
Annual reviews are no longer enough to keep up with today’s fast-evolving threats. Vulnerabilities can be exploited within days of disclosure, making real-time monitoring essential [6]. Use tools like security ratings, threat intelligence feeds, and vulnerability alerts to stay ahead [6][4][19]. Apply Zero Trust principles by enforcing least-privilege access, multi-factor authentication, and network segmentation for vendor connections [6].
Establish a feedback loop to address security gaps promptly. Track metrics like Mean Time to Remediate (MTTR), patch timelines for critical vulnerabilities, and SLA performance trends to identify areas for improvement [18][6]. Additionally, include key vendors in annual incident response drills to ensure coordinated action during potential breaches [6][19].
Recent incidents highlight the risks of vendor security failures. In June 2024, a ransomware attack on CDK Global disrupted operations for 15,000 automotive dealerships in North America, showcasing the dangers of relying heavily on a single critical vendor [19]. Similarly, the May 2023 MOVEit zero-day vulnerability caused global data breaches, demonstrating how a single unpatched flaw can lead to widespread consequences [19].
To streamline vendor security management, companies like Phoenix Strategy Group offer automated evidence collection systems. These tools use APIs to pull updated SOC 2 reports and certifications, reducing the need for manual follow-ups [18][4]. By combining automation with strategic oversight, businesses can ensure strong IT vendor security while staying focused on growth. For many organizations, this level of strategic oversight is often managed by a fractional CFO who can align security investments with broader financial goals.
6. Prioritize Risks and Plan Remediation
Risk Identification and Categorization
After completing initial vendor assessments, the next step is to prioritize risks so you can focus your remediation efforts where they’ll have the greatest impact. Vendor-related risks can vary widely, and their importance often depends on the potential consequences. For example, 60% of data breaches stem from third-party vulnerabilities [20]. To get started, calculate each vendor's inherent risk score, which represents the baseline risk before any controls are applied [2]. This score should take into account factors like the sensitivity of the data the vendor handles, the level of network access they have, and their role in keeping your business running smoothly. These elements will help you determine how urgently remediation is needed [4,36].
For an objective prioritization process, a quantitative formula can be helpful:
Risk Score = (Threat Likelihood × Business Impact) / Control Effectiveness [20].
Vendors that deal with regulated data - such as personally identifiable information (PII) or protected health information (PHI) - or those with extensive network access or critical operational roles should be classified as "critical" or "high-risk" [4,36]. From there, segment vendors into tiers (e.g., critical, medium, low) based on their risk scores [40,7]. These tiers can then guide your contractual terms and remediation strategies.
Contractual Clarity and Compliance
Once you’ve categorized risks, it’s crucial to ensure that vendor contracts reflect these priorities and hold vendors accountable. Contracts should include specific provisions such as remediation deadlines, incident reporting requirements, and penalties for non-compliance [38,7]. For high-risk issues, establish escalation paths that clearly define who to contact and what steps to follow if deadlines aren’t met [22].
"Remediation means proactively correcting vulnerabilities, enforcing accountability, and building lasting resilience." - Shweta Dhole, TrustCloud [22]
Additionally, contracts should include exit clauses that outline obligations for data return or destruction if a vendor fails to meet security requirements [21]. Tie these remediation plans to your existing monitoring frameworks to maintain consistency across your risk management strategy. Once these contractual obligations are defined, continuous monitoring will help ensure that remediation efforts are effective.
Monitoring and Continuous Improvement
A remediation plan is only as good as its execution. To keep everything on track, maintain a risk register that documents each risk, its remediation plan, and progress updates [39,41]. Use ongoing monitoring, vulnerability scans, and penetration tests to confirm that remediation efforts are working as intended [22].
Since only 27% of organizations focus on ongoing monitoring, it’s clear that consistent tracking is critical [8]. Strengthen your efforts by incorporating real-time threat intelligence and security rating alerts to catch vulnerabilities as they emerge [6]. Track key metrics like vendor incident response times, the speed of patching critical vulnerabilities (e.g., within 48 hours), and unresolved audit findings. These insights will help you spot trends and refine your program over time [7,39].
7. Connect Third-Party Risk to Enterprise Risk Management
Risk Identification and Categorization
To effectively manage third-party risks, weave them into your broader enterprise risk management (ERM) framework. Categorize vendor-related exposures alongside internal risks - strategic, operational, financial, compliance, and cybersecurity. By mapping these vendor relationships within your overall risk landscape, you gain a clearer, more unified view of your organization's vulnerabilities across the extended enterprise.
Why is this important? Over 60% of data breaches involve third-party elements, and these breaches are 40% more expensive to address compared to internal incidents [24]. Yet, only 16% of organizations feel confident in their ability to handle third-party risks effectively [23]. The issue often lies in fragmented management, where procurement, IT, and legal teams address vendor risks in silos. This disjointed approach weakens oversight. By centralizing these efforts, you ensure that vendor risks inform expert growth strategies rather than being treated as isolated issues.
When done right, this consolidated risk mapping can lead to smoother oversight across all departments.
Monitoring and Continuous Improvement
Centralizing vendor risk oversight through internal risk categories is becoming the norm - 90% of organizations are now adopting this approach to improve consistency and efficiency [24]. To make this work, form a cross-functional steering committee with representatives from procurement, IT security, compliance, and legal. This group should oversee vendor risks and report findings to enterprise risk governance bodies.
"TPRM programs achieve strategic value when they become integral to enterprise decision-making, moving beyond isolated compliance functions." - Archer Integrated Risk Management [23]
To further dismantle operational silos, use standardized frameworks like the NIST Cybersecurity Framework or ISO 27001. These provide a shared vocabulary for discussing and addressing risks. When presenting to executives or board members, focus on translating technical vendor risks into business-oriented metrics - like potential revenue loss, reputational harm, or customer dissatisfaction. This approach ensures vendor risk assessments align with your organization's risk appetite, preventing one department from greenlighting risks that conflict with enterprise-level priorities.
Third-Party Risk Management 101: Assess, Monitor, and Mitigate: The Core Components of TPRM
Conclusion
Managing third-party risks isn't optional - it's a critical part of running a successful business. The seven practices discussed here offer a clear path to safeguarding your organization as it grows. From pinpointing and evaluating vendor risks to embedding oversight into your overall risk management strategy, each step strengthens your ability to handle challenges effectively.
Third-party relationships are linked to about 33% of security incidents [6]. With the average organization juggling 5,800 vendors [27], and 37% of risk and compliance professionals admitting their approach to third-party risk is either nonexistent or purely reactive [25], the need for structured oversight is clear. On top of that, vendor-related data breaches cost an average of $370,000 more than internal breaches [26]. These numbers highlight why a solid vendor management framework is essential - not just for security, but for supporting growth as your vendor network expands.
Industry leaders emphasize this proactive approach:
"Third party risk management can no longer be regarded as a point-in-time focused exercise, but a critical daily function that manages risk throughout a vendor's lifecycle." - Cedar Rose [1]
Moving from reactive compliance to proactive resilience takes effort but pays off significantly. Start by categorizing vendors based on their importance to your operations for more focused assessments. Automate evidence collection to save time and reduce manual tasks. Use Zero Trust principles to secure vendor connections, and ensure every contract includes a clear exit strategy. These aren't just guidelines - they're essential steps for building a strong foundation to support your growth.
Organizations with robust, business-aligned cyber risk programs are 4.5 times more likely to monitor vendor relationships continuously [4]. This kind of foresight offers a real competitive edge. As the third-party risk management market grows toward an estimated $11.34 billion by 2028 [1], adopting these practices now will help protect your brand, maintain customer trust, and turn vendor oversight into a strategic advantage. By aligning third-party risk management with your overall business goals, you can transform compliance from a requirement into a tool for driving success.
FAQs
How do I decide which vendors are high-risk?
To spot vendors that might pose risks, consider elements like cybersecurity measures, financial stability, regulatory compliance, and operational reliability. Pay attention to Key Risk Indicators (KRIs) such as past security breaches, financial troubles, service interruptions, and compliance issues. Keep a detailed vendor inventory and sort vendors into risk categories. This helps you focus your monitoring efforts and address potential issues more effectively. Regular evaluations are crucial to staying ahead of vulnerabilities.
What proof should I ask vendors for during onboarding?
When bringing a new vendor on board, it's crucial to ask for proof of their security and compliance measures. Key documents to review include details about their data security protocols, risk assessments, and evidence of compliance with relevant standards.
Take the time to verify their security controls, examine their incident response plans, and ensure they adhere to any contractual agreements and service level agreements (SLAs). Conducting a thorough due diligence process helps confirm that their policies align with your organization’s expectations and requirements.
How can I monitor vendors continuously without extra work?
To make continuous vendor monitoring more efficient, concentrate on risk-based prioritization, regular reassessments, and focused evaluations after significant events. These approaches cut down on manual work while keeping a close eye on vendor activities. Using automated tools and clear reporting can further simplify the process, offering insights into vendor performance and risks without overwhelming your team. These methods help you stay on top of monitoring without adding unnecessary complexity.




