How End-to-End Encryption Secures Payments

End-to-end encryption (E2EE) is essential for protecting payment data in an increasingly digital world. It ensures that sensitive information remains encrypted from the moment it's entered by the customer until it reaches the payment processor. This approach eliminates vulnerabilities during transmission, storage, and processing, safeguarding against cyberattacks and insider threats.
Key Points:
- Data Protection: E2EE encrypts payment data immediately, making it unreadable to attackers even if intercepted.
- Reduced Breach Risks: Only 4% of breaches affect systems using encryption, significantly lowering exposure.
- Customer Confidence: Secure payments boost trust, with 77% of shoppers abandoning carts if security feels inadequate.
- PCI DSS Compliance: E2EE simplifies meeting standards, reducing audit scope and potential fines.
- Fraud Prevention: Protects against external attacks and insider misuse by keeping data encrypted throughout the process.
E2EE is a critical measure for businesses aiming to secure transactions, protect customer trust, and minimize financial and reputational risks. By combining encryption with other security measures like tokenization and TLS, companies can build a safer and more reliable payment ecosystem.
How End-to-End Encryption Protects Digital Payments
sbb-itb-e766981
How End-to-End Encryption Protects Payment Data
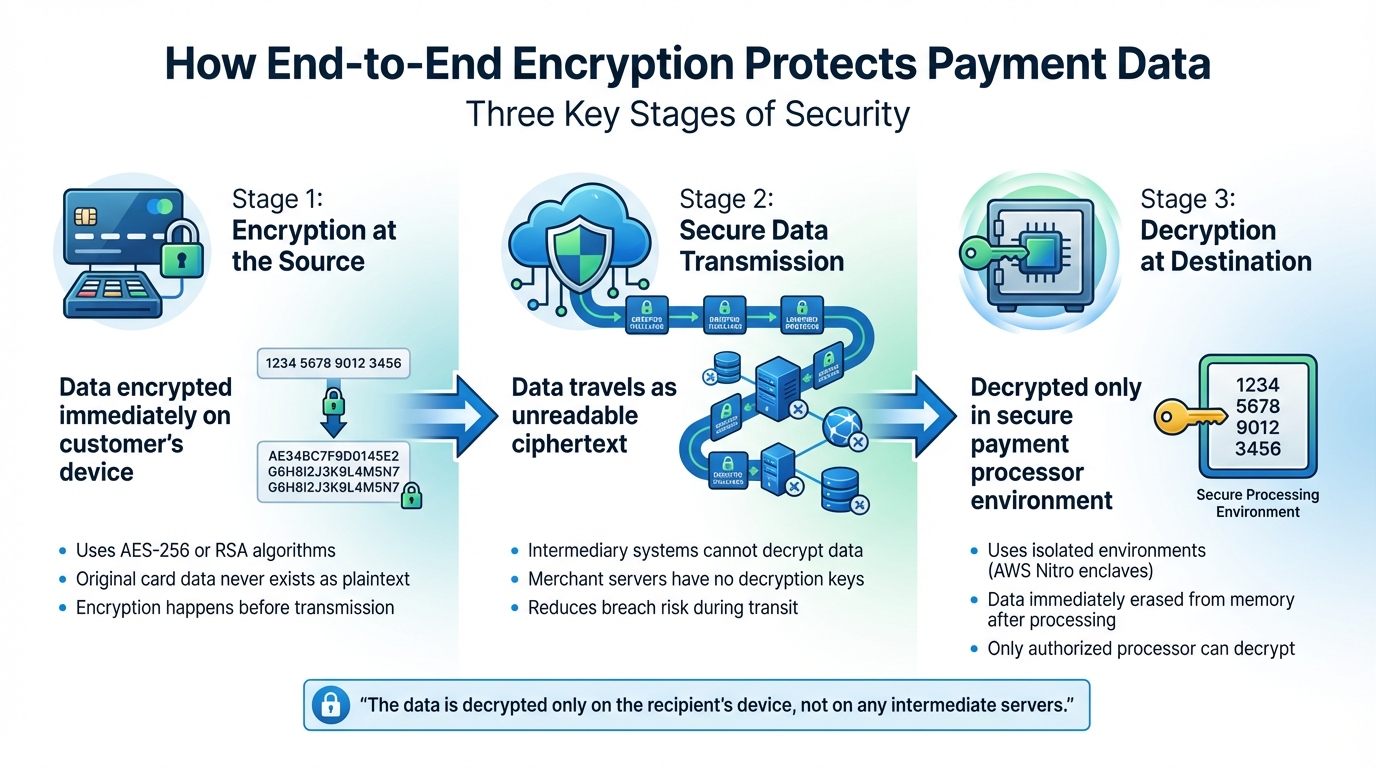
How End-to-End Encryption Protects Payment Data in 3 Stages
End-to-end encryption (E2EE) safeguards payment data by turning it into ciphertext from the moment it's entered until it reaches the payment processor [1]. Unlike older encryption methods that protect data only at certain points, E2EE ensures the information stays encrypted throughout its entire journey.
"Encryption transforms sensitive payment data... into unreadable code, protecting it from unauthorised access. Only those with the right decryption keys can convert this information back into a usable format." [2]
This protection unfolds in three key stages: encryption at the source, secure transmission, and decryption at the destination. Together, these stages create an unbroken chain of security.
Encryption at the Source
As soon as a customer enters their card details into a payment form or swipes their card, the data is encrypted on the device itself before transmission [1][2]. Algorithms like AES-256 or RSA are commonly used for this purpose [2][7]. AES-256, in particular, is known for its strong defense, with no practical attacks reported [2]. The encryption process uses either a public key to scramble the data or a shared secret for local encryption [3]. This ensures that the original card information never exists as plaintext outside the customer’s device, addressing vulnerabilities that could lead to data interception.
Secure Data Transmission
Once encrypted, the payment data travels as ciphertext through networks, servers, and systems. Importantly, intermediary systems, such as merchant servers, do not have the decryption keys and cannot access the data [1][2]. This means transactions can be processed without exposing sensitive information, which not only reduces the risk of breaches but also simplifies compliance with security standards. For businesses scaling rapidly, managing these security costs and compliance requirements often benefits from the strategic oversight of fractional CFO services.
Decryption at the Destination
The encrypted data can only be read once it reaches the payment processor’s highly secure environment [2]. Many modern systems rely on isolated environments like AWS Nitro enclaves to handle decryption. These systems decrypt the data and then immediately erase it from memory after processing [3]. By limiting decryption to this secure environment, the process ensures that the data remains protected every step of the way.
"The data is decrypted only on the recipient's device, not on any intermediate servers." [2]
Key Benefits of End-to-End Encryption in Payments
End-to-end encryption (E2EE) plays a vital role in securing payment systems while also delivering measurable advantages for businesses.
By strengthening data protection, E2EE ensures payment security and provides several key benefits.
Reducing Data Breach Risks
Even if hackers manage to intercept payment data, end-to-end encryption ensures they can’t use it. Since 2013, over 14.7 billion records have been stolen or lost, yet only 4% of breaches affected systems that employed encryption [8]. To put it in perspective, data breaches occur at a staggering rate of 73 records per second globally [8]. With E2EE, attackers only gain access to unreadable ciphertext, making the data useless.
Considering that the average cost of a data breach reached $4.45 million in 2023 [10], investing in end-to-end encryption is not just about security - it’s a smart financial decision to mitigate risks.
Building Customer Trust
A secure payment process fosters customer confidence and loyalty. By late 2020, nearly 80% of U.S. shoppers were using some form of digital payment [9]. Knowing their payment information is encrypted reassures customers and strengthens trust.
"Trust in the digital economy is built on security." - Omvaris Limited [4]
This trust directly impacts business outcomes. It leads to higher conversion rates, repeat business, and positive word-of-mouth. With cyberattacks rising by 31% between 2020 and 2021 and phishing attacks targeting 83% of organizations in 2021 - a 26% jump from the previous year [9] - companies that prioritize security stand out in a competitive and increasingly risky environment.
Meeting PCI DSS Compliance Requirements
End-to-end encryption simplifies compliance with Payment Card Industry Data Security Standards (PCI DSS) by ensuring cardholder data is unreadable. It specifically addresses two critical requirements:
- Requirement 3: Protecting stored data
- Requirement 4: Securing data during transmission over public networks [10]
Failing to meet these standards can result in steep fines, ranging from $5,000 to $100,000 per month [10].
E2EE also reduces the scope of PCI DSS audits. Businesses using PCI-validated encryption solutions, such as Point-to-Point Encryption (P2PE), often qualify for shorter Self-Assessment Questionnaires (SAQs), saving both time and money during annual compliance checks.
"By using a PCI-approved P2PE solution, businesses can ensure that sensitive payment information is never exposed within their systems. This reduces the scope of compliance efforts and minimizes the complexity of securing customer data." - onemoneyway.com [5]
How End-to-End Encryption Prevents Fraud and Insider Threats
Payment fraud is on the rise - global losses are expected to surpass $40 billion by the end of 2025 [6]. End-to-end encryption (E2EE) serves as a powerful shield, protecting sensitive data from external attacks and internal breaches by securing vulnerabilities across multiple fronts.
Protection Against External Cyber Attacks
With E2EE, data is encrypted immediately at checkout, making it unreadable to cybercriminals. Even if attackers manage to intercept information through methods like man-in-the-middle attacks, all they’ll capture is indecipherable ciphertext.
The strength of this defense lies in key isolation. Using public key cryptography, decryption keys are exchanged directly between the sender and recipient. This approach ensures that without access to the keys, attackers are left empty-handed - they can neither use nor sell the stolen data [11][4].
"In any payment ecosystem, trust is transactional. The moment a breach occurs, trust evaporates. Businesses must embed advanced security tools at the architectural level - before innovation introduces new risks." - Eric Hannelius, Fintech Expert [6]
This level of protection is especially vital for small and midsize businesses, which are prime targets for cyberattacks. These businesses account for 43% to 60% of all cyberattacks, and unfortunately, 60% of those affected shut down within six months [12]. E2EE provides a crucial layer of defense, helping to safeguard their survival.
While E2EE effectively counters external threats, it also plays a key role in addressing risks from within.
Reducing Insider Risks
Beyond shielding against external attacks, E2EE limits internal vulnerabilities by ensuring that plaintext data is only accessible at the final destination or within secure hardware enclaves [12][3]. This means even someone with direct access to a database cannot view sensitive payment information - it remains encrypted.
Systems that implement dual-custody with Shamir Secret Sharing take this a step further. Keys are divided into fragments, so no single administrator can reconstruct them or independently access sensitive data [3]. Additionally, cryptographic keys are tightly controlled, with access granted on a "need-to-know" basis and protected by two-factor authentication [12].
"End-to-end encryption (E2EE) effectively neutralizes [insider] threats. Even if the data is intercepted or improperly stored, it remains unreadable without the corresponding cryptographic key." - Omvaris Limited [4]
Modern E2EE systems also employ memory wiping within isolated environments like AWS Nitro enclaves. Here, decryption occurs securely, and memory is erased immediately afterward [3]. By ensuring that application servers never handle raw customer data, these measures drastically reduce the risk of insider fraud, creating a secure and resilient payment ecosystem.
Implementing End-to-End Encryption for Growth-Stage Companies
For mid-market businesses, setting up end-to-end encryption is entirely achievable with the right strategy. Start by building a strong foundation and layering additional security measures. This structured approach ensures payment data stays secure without disrupting daily operations.
Choosing the Right Encryption Solutions
Before diving into encryption technology, take a thorough look at your current infrastructure. Older systems may need significant updates to meet modern encryption standards [1]. For growth-stage companies, it's critical to prioritize hardware with tamper-resistant features and support for AES-256 encryption - a proven standard in the industry.
For specific use cases:
- Use P2PE (Point-to-Point Encryption) for physical retail environments.
- Opt for E2EE (End-to-End Encryption) for online transactions [5].
"End-to-end encryption is more than a technology. It is a trust mechanism that signals responsibility, integrity, and foresight." - Irene Risner, Author [1]
If the technical aspects feel overwhelming, seeking expert guidance can simplify the decision-making process.
Working with Financial Advisory Experts
Encryption implementation often requires specialized expertise, making collaboration with financial advisors a smart move. These experts can help integrate encryption into your existing systems, manage secure key rotation, and ensure compliance with PCI DSS standards [1][8]. For example, Phoenix Strategy Group provides advisory services tailored to these needs.
Advisors also assist in determining the best fit for your operations - whether that's end-to-end encryption, P2PE, or PCI-validated P2PE [8]. With only 4% of data breaches occurring in systems where encryption was in place [8], partnering with professionals who understand both technical and regulatory complexities can significantly lower your risk.
Combining Encryption with Other Security Measures
Once you've implemented encryption and partnered with experts, take your security to the next level by adding complementary measures. End-to-end encryption is most effective when integrated into a broader, multi-layered security strategy. Consider the following:
- Transport Layer Security (TLS): Protects data in transit.
- SSL/TLS Handshakes: Establishes secure connections between browsers and servers.
- Tokenization: Replaces sensitive card data with non-sensitive equivalents.
To further reduce risks, automate key rotation using centralized Key Management Services (KMS) [1][2]. Ensure that all internal API calls use modern protocols like TLS 1.2 or higher, maintaining consistent security across your systems [13]. Regular security audits are also essential to identify and address vulnerabilities early [1].
"Encryption is more than a technical safeguard – it gives your customers confidence to click 'Pay Now' with peace of mind." - Airwallex [2]
Conclusion
End-to-end encryption (E2EE) plays a crucial role in safeguarding payment data at every step of the transaction process - starting from data entry, through secure transmission, and finally to authorized decryption. With global payment fraud losses expected to surpass $40 billion by the end of 2025 [6], the need for robust security measures is more pressing than ever for companies looking to scale.
E2EE not only reduces PCI DSS compliance scope but also strengthens customer confidence and shields your brand from the devastating effects of data breaches. As Shane Curran, Founder & CEO of Evervault, aptly says:
"Encryption becomes the payment flow's safety net against data breaches and credit card fraud" [3].
To maximize these benefits, businesses need a well-thought-out encryption strategy. This often involves integrating secure hardware with AES-256 encryption, leveraging automated key management via Hardware Security Modules, and incorporating additional safeguards like tokenization and TLS protocols. However, managing cryptographic keys and staying compliant can be complex, making expert support invaluable. Phoenix Strategy Group specializes in helping growth-stage companies design encryption strategies that align with both their technical needs and business expansion goals. Their advisory services allow businesses to focus on scaling while ensuring payment security remains a top priority.
Protecting payment systems is no longer just an IT responsibility - it's a business imperative that directly impacts customer trust, operational effectiveness, and competitive positioning. Start securing your payment infrastructure today to provide your customers with the assurance that their data is safe from start to finish.
FAQs
Does E2EE protect card data if a merchant’s server is hacked?
End-to-end encryption (E2EE) secures card data while it’s being transmitted, but it doesn’t protect the data once it’s decrypted by the payment processor. If a hacker breaches a merchant’s server, any unencrypted data stored there remains vulnerable. In short, E2EE is excellent for safeguarding data in transit but doesn’t offer protection for data stored on compromised servers.
How is E2EE different from TLS and tokenization?
End-to-end encryption (E2EE) ensures that data stays encrypted from the moment it’s entered until it reaches the payment processor. This means only the intended parties can access the information. While TLS (Transport Layer Security) protects the communication channel, it doesn’t offer encryption that spans the entire journey of the data.
On the other hand, tokenization replaces sensitive information with non-sensitive tokens, reducing the risk of exposure if the data is intercepted. However, tokenization doesn’t encrypt the data itself. E2EE stands out by maintaining encryption consistently throughout the entire process, offering robust protection.
Will E2EE reduce my PCI DSS scope and audit effort?
Yes, end-to-end encryption (E2EE) can help narrow your PCI DSS scope and make audits easier. By encrypting cardholder data right at the point of interaction and ensuring it stays encrypted until it's decrypted, E2EE reduces the systems and processes subject to PCI compliance checks. This approach simplifies the audit process significantly.




