Multi-Cloud Key Management for SaaS Companies

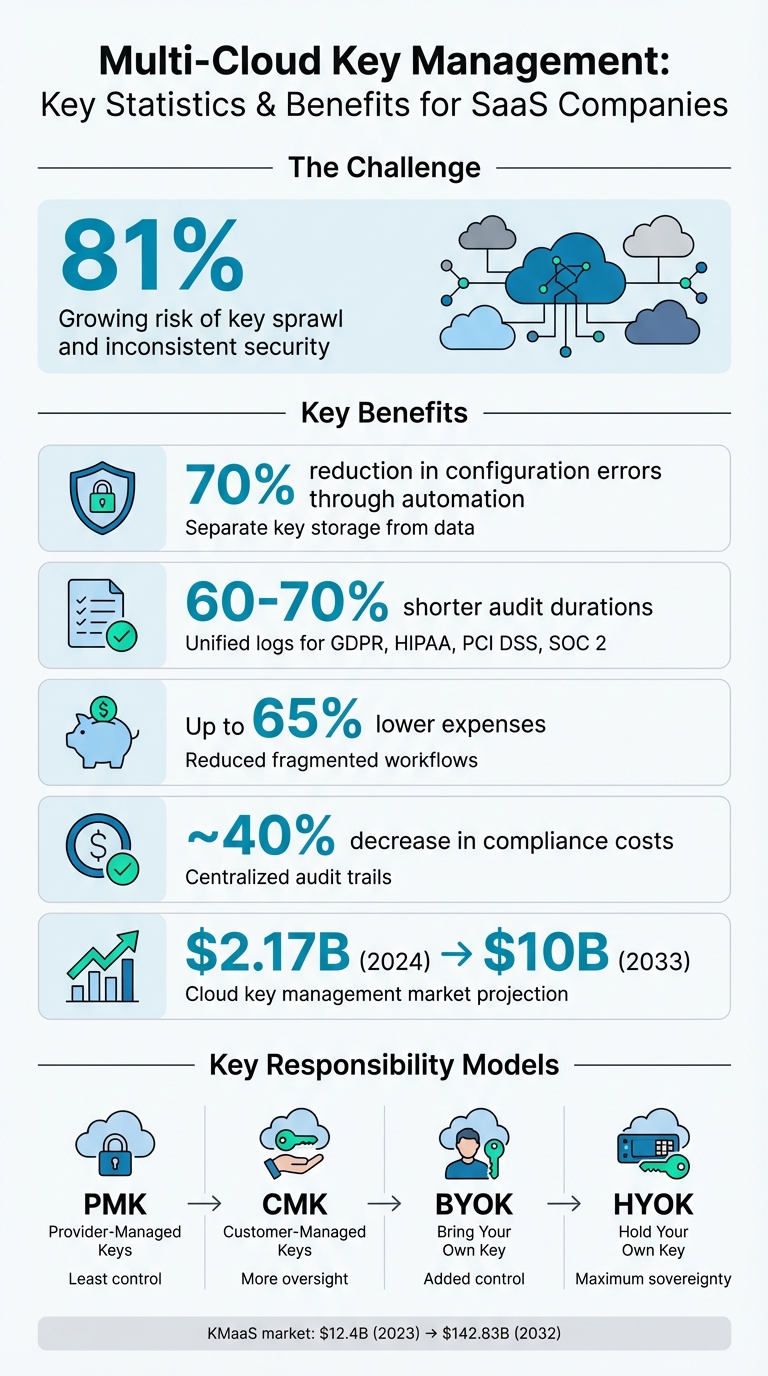
Managing encryption keys across multiple cloud platforms is a growing challenge for SaaS companies. With 81% of them using multiple cloud providers, the risks of "key sprawl" and inconsistent security are increasing. Here's how centralized multi-cloud key management can solve these issues:
- Centralized Control: Manage encryption keys from a single platform, reducing errors and improving security.
- Improved Security: Store keys separately from data to minimize risks during breaches.
- Compliance Made Simpler: Consolidate logs and prove adherence to regulations like GDPR, HIPAA, and PCI DSS.
- Operational Efficiency: Automate key tasks like rotation and permissions updates to save time and reduce manual errors.
- Future-Ready Systems: Ensure compatibility across cloud platforms and prepare for evolving security standards.
Multi-Cloud Key Management Benefits and Statistics for SaaS Companies
Akeyless Encryption & Multi Cloud KMS Video
sbb-itb-e766981
Benefits of Multi-Cloud Key Management for SaaS Companies
Multi-cloud key management offers SaaS companies a range of benefits, particularly when it comes to securing data, meeting compliance needs, and streamlining operations.
Stronger Security and Data Protection
Storing encryption keys separately from the data they protect is a smart way to enhance security. This separation ensures that even if one cloud provider is breached, your encrypted data remains safe [6] [1]. By distributing keys across multiple providers, you eliminate single points of failure. For example, if one platform suffers an outage or breach, your other data remains unaffected [6] [8].
Solutions that use FIPS 140-2 Level 3 or Level 4 validated Hardware Security Modules (HSMs) provide an extra layer of protection for cryptographic operations [1] [7] [8]. Additionally, automating key lifecycle management tasks - like key rotation and updating permissions - can cut configuration errors by up to 70% [2].
Easier Compliance with Data Regulations
Managing keys across multiple clouds through a centralized system makes regulatory compliance much more straightforward. By consolidating audit logs from platforms like AWS, Azure, and Google Cloud into one control plane, you can easily demonstrate adherence to standards such as GDPR, HIPAA, SOC 2, and PCI DSS [1] [7]. This unified approach not only simplifies audits but also reduces the administrative burden that comes with fragmented systems.
It also helps meet data sovereignty requirements by keeping encryption keys within specific geographic regions, such as the European Economic Area, to comply with GDPR and Schrems-II mandates [7]. Beyond regulatory needs, centralizing key management improves operational efficiency, making it easier to handle complex multi-cloud environments.
Better Operations and Scalability
Centralized multi-cloud key management replaces tedious, manual processes with automation. Instead of switching between separate cloud provider consoles, you can manage the entire key lifecycle - generation, rotation, and deletion - through a single interface [1] [7]. This efficiency extends to development workflows, with RESTful APIs and support for standards like PKCS#11 and KMIP enabling smooth integration into CI/CD pipelines [1] [7].
Tasks that previously required manual effort, such as downloading and wrapping keys for Bring Your Own Key (BYOK) processes, can now be handled with a single API request [1]. Moreover, adopting crypto-agility ensures your infrastructure is ready for evolving security standards, including post-quantum cryptography, without requiring a complete overhaul [2] [3].
As Nishank Vaish from Fortanix explains, "A strong key management strategy isn't just about control; it's about flexibility and readiness for whatever comes next" [2].
These advantages make multi-cloud key management a compelling choice for SaaS companies looking to strengthen their security, simplify compliance, and streamline operations.
Core Components of a Multi-Cloud Key Management Strategy
Creating a reliable multi-cloud key management system involves three main elements. These address security challenges, operational needs, and regulatory compliance for SaaS companies.
Centralized Key Management
A centralized control plane is the heart of any multi-cloud strategy. Instead of juggling between AWS, Azure, and Google Cloud interfaces, you can manage the entire lifecycle of your encryption keys - generation, storage, rotation, and retirement - from one unified platform [7][1][6]. This setup simplifies operations and reduces the risk of manual errors caused by switching between systems.
One major security benefit is the ability to separate duties. By storing encryption keys in an environment separate from the data they protect, even if a cloud storage system is breached, attackers can’t access your encryption keys [7][1][6]. For maximum security, store keys in FIPS 140-2 Level 3-certified Hardware Security Modules (HSMs) [7][1]. A centralized system also ensures consistent enforcement of granular access policies, such as requiring multiple authorized users to approve sensitive actions like key deletion (quorum approvals) [7][1].
Next, let’s explore how integrating with major cloud providers strengthens this centralized approach.
Integration with Major Cloud Providers
Your key management system should integrate smoothly with native cloud services like AWS KMS, Azure Key Vault, and Google Cloud KMS while maintaining independence from any single vendor. Modern solutions often support standardized protocols like the Key Management Interoperability Protocol (KMIP) to ensure compatibility across platforms [5]. They also include RESTful APIs, making it easy to embed key management directly into DevOps workflows, containers, and CI/CD pipelines [7][1].
There are three common architectural patterns to consider:
- Federation Layer: Provides unified API access to keys stored in native cloud services, minimizing the need for migration.
- Dedicated Vault: Migrates all keys to a cloud-agnostic system that syncs with your deployment targets, offering strong vendor independence.
- Hybrid Model: Combines native services for infrastructure-specific secrets with a dedicated vault for application-level API keys [9].
As multi-cloud adoption grows, picking the right integration pattern is crucial for maintaining both security and operational ease.
Finally, let’s look at how compliance and audit readiness tie everything together.
Compliance and Audit Readiness
Centralized audit logging simplifies compliance by automatically consolidating logs from AWS, Azure, and Google Cloud into a single interface. This makes it easier to demonstrate compliance with regulations like GDPR, HIPAA, SOC 2, and PCI DSS [2].
Geographic sovereignty is another key factor. Your system should provide the ability to define and prove that encryption keys remain in specific regions, such as the European Economic Area, to meet data residency requirements [7]. With the cloud key management market expected to grow from $2.17 billion in 2024 to nearly $10 billion by 2033 [3], features like automated key rotation, expiration alerts, and role-based access controls have become standard requirements rather than optional extras.
How to Implement Multi-Cloud Key Management
Setting up multi-cloud key management involves three main phases: assessment, selection, and deployment.
Assess Your Business Requirements
Start by creating an inventory of all encryption keys, certificates, and endpoints currently in use across platforms like AWS, Azure, Google Cloud, and any on-premises systems you maintain [2]. This process helps you avoid key sprawl and highlights any security gaps that need attention.
Next, identify the regulations that apply to your organization, such as GDPR, HIPAA, PCI DSS, or FIPS 140-3, as each has specific requirements for managing encryption keys [4]. Based on your organization's risk tolerance and internal expertise, decide on a key responsibility model. Here’s a quick breakdown of the options:
- Provider-Managed Keys (PMK): Simplifies operations but offers limited control.
- Customer-Managed Keys (CMK): Provides more oversight, though the cloud provider still stores the keys.
- Bring Your Own Key (BYOK): Lets you generate and import your keys for added control.
- Hold Your Own Key (HYOK): Delivers maximum sovereignty, as your keys never leave your infrastructure, ensuring the cloud provider cannot decrypt your data [4].
Also, consider whether your team has the capability to securely manage a Hardware Security Module (HSM) infrastructure or if outsourcing to a Key Management as a Service (KMaaS) model is a better option. The KMaaS market, valued at $12.4 billion in 2023, is projected to grow to $142.83 billion by 2032 [8].
Once you’ve defined your encryption inventory and compliance requirements, you’re ready to explore tools that align with your multi-cloud setup.
Choose the Right Tools and Platforms
Your requirements will guide you in selecting tools that automate and secure the key management lifecycle. Opt for solutions that support the Key Management Interoperability Protocol (KMIP) to ensure compatibility across cloud platforms and minimize vendor lock-in [5]. Automation is key - look for platforms that handle the full lifecycle of keys, including generation, distribution, rotation, and destruction. This approach helps eliminate manual errors, which account for up to 70% of configuration mistakes [2].
Here are some standout platforms for multi-cloud environments:
- HashiCorp Vault (Enterprise and HCP): Features a Key Management Secrets Engine to manage the entire key lifecycle [11].
- Fortanix Data Security Manager: A unified SaaS platform supporting AWS, Google Cloud, and Azure, with FIPS 140-2 Level 3-certified HSMs to keep keys separate from data [7].
- Akeyless Identity Security Platform: Uses Distributed Fragments Cryptography to manage keys across clouds with zero-knowledge assurance. Users report a 70% reduction in maintenance time compared to traditional solutions [12].
Real-world examples demonstrate the effectiveness of these tools. For instance, in June 2025, InfoCert, a European digital trust service provider, adopted a KMaaS solution for their MongoDB environment. This move eliminated the need for extra on-premises software while maintaining FIPS 140-2 certified security [8]. Similarly, a Canadian telecommunications company centralized encryption for thousands of servers using KMIP, integrating with VMware vSAN and Ansible for consistent encryption-at-rest [8].
Deploy and Monitor Your Solution
After assessing your needs and selecting the right platform, it’s time to deploy and maintain your key management system. Use Infrastructure as Code (IaC) tools to connect the platform to each cloud provider’s native services, ensuring consistent configurations across multiple regions [10]. For sensitive operations, implement quorum approval policies, requiring multiple user authorizations for actions like key deletion [1].
From the start, set up centralized audit logging to consolidate logs from AWS, Azure, and Google Cloud into one interface [2]. Automate key rotation schedules and configure expiration alerts to maintain security without manual oversight.
Continuous monitoring is crucial. Modern platforms provide real-time dashboards that track which applications access specific keys, when rotations occur, and any failed authentication attempts. This level of visibility ensures compliance readiness and allows you to address potential security issues before they escalate.
Conclusion
Multi-cloud key management is becoming essential for SaaS companies looking to scale securely. By unifying key management across multiple cloud platforms, businesses can protect sensitive data, meet regulatory requirements, and support their growth objectives. The real question isn't whether to adopt this approach but how quickly it can be implemented.
This approach also brings notable cost savings. Centralized key management can lower expenses by up to 65% by reducing fragmented workflows and cutting down engineering overhead [9]. On the compliance front, unified audit trails can shorten audit durations by 60–70% and decrease overall compliance costs by about 40% [2]. These efficiencies free up valuable resources that can be redirected toward product innovation and acquiring new customers.
Key Takeaways for SaaS Entrepreneurs
Here’s a quick recap of the most important steps:
- Start with a comprehensive mapping of encryption assets. Identify all encryption keys, certificates, and endpoints, and align them with the specific regulations your business must follow, such as GDPR, HIPAA, or PCI DSS. Each regulation has distinct requirements for managing encryption keys.
- Focus on separation and automation. Always store encryption keys in a separate environment from the data they protect. Automate the key lifecycle process to minimize manual errors, which account for up to 70% of configuration mistakes [2].
Rob Westervelt of IDC emphasizes: "Centralized key management is the linchpin for data privacy and sovereignty in the era of multicloud" [8].
- Plan for future flexibility. The cloud key management market is expected to grow from $2.17 billion in 2024 to nearly $10 billion by 2033 [3]. As multi-cloud environments grow more complex and data security becomes increasingly critical, choose platforms that support KMIP to avoid vendor lock-in. Look for crypto-agility features to prepare for emerging threats like post-quantum computing. Your key management strategy should align with the long-term vision of your business.
For SaaS companies tackling these challenges, Phoenix Strategy Group provides financial and strategic advisory services. They specialize in helping growth-stage businesses scale securely, maintain compliance, and navigate future challenges with expert data engineering and strategic planning.
FAQs
When should we move from single-cloud KMS to multi-cloud key management?
Transitioning to multi-cloud key management is essential when adopting a multi-cloud strategy that spans multiple providers. This shift becomes particularly important if you're dealing with challenges like key sprawl, inconsistent encryption practices, or heightened regulatory compliance risks.
A unified key management system offers several advantages: it centralizes control, automates key rotation, enforces strict access controls, and helps you avoid being locked into a single vendor. As your cloud environment grows more complex and security or compliance needs surpass the capabilities of single-cloud solutions, making this transition becomes not just beneficial, but necessary.
How do BYOK and HYOK differ, and which one fits our risk and compliance needs?
BYOK (Bring Your Own Key) allows organizations to create and upload their own encryption keys to a cloud provider. While this approach gives businesses control over key lifecycle operations, the keys themselves are stored within the provider's infrastructure.
On the other hand, HYOK (Hold Your Own Key) keeps encryption keys completely outside the cloud provider's environment. This setup provides a higher level of security and compliance, making it ideal for protecting highly sensitive data. HYOK is particularly suited for organizations with stricter regulatory requirements.
In comparison, BYOK is simpler to implement but offers less control over the encryption keys compared to HYOK.
What’s the simplest way to prove key residency and audit readiness across AWS, Azure, and Google Cloud?
Centralized key management solutions provide an easy way to handle encryption keys. These tools bring everything together in one secure interface, offering unified control, clear visibility, and audit logs for encryption keys across different platforms. By consolidating encryption processes, they help ensure compliance and simplify the management of sensitive data.




