Ultimate Guide to Blockchain and GDPR Compliance

Blockchain and GDPR often clash due to their opposing principles. Blockchain's immutability conflicts with GDPR's "right to erasure", while its decentralized nature complicates accountability under GDPR's data controller requirements. Businesses must carefully balance blockchain's strengths with GDPR obligations to avoid penalties of up to €20 million or 4% of global annual revenue.
Key Takeaways:
- Blockchain data is permanent, making GDPR's "right to erasure" difficult to implement.
- GDPR requires a clear "data controller", but blockchain's decentralized structure complicates this.
- Public blockchains pose higher compliance risks compared to private or hybrid systems.
- Storing personal data off-chain, using cryptographic erasure, and leveraging privacy tools like zero-knowledge proofs can help align blockchain with GDPR.
To comply, businesses should:
- Conduct a Data Protection Impact Assessment (DPIA) before using blockchain.
- Use off-chain storage for personal data and only store pseudonymous or encrypted references on-chain.
- Adopt permissioned or hybrid blockchain models for better control and accountability.
- Regularly audit and monitor blockchain systems for compliance with GDPR standards.
The solution lies in designing blockchain systems that prioritize privacy and ensure compliance while maintaining their core functionality.
Delete the Chain? Privacy, Regulation, and the Future of Public Blockchains in Europe
sbb-itb-e766981
GDPR Compliance Challenges in Blockchain
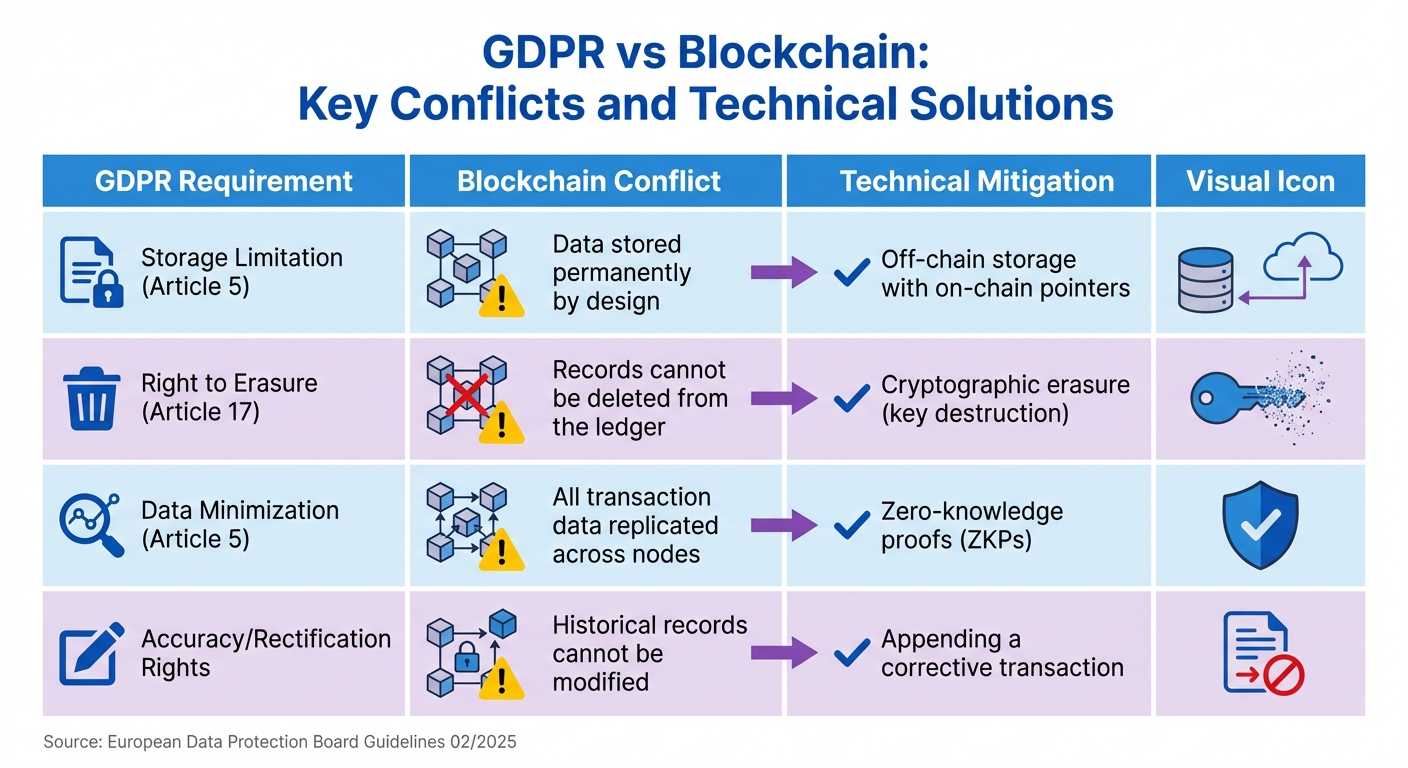
GDPR vs Blockchain: Key Conflicts and Technical Solutions
Blockchain's fundamental characteristics often clash with GDPR requirements, creating significant hurdles that need to be addressed before implementation. Below, we explore three key areas where these conflicts arise and the regulatory issues they present.
Permanent Records vs. Right to Erasure
The GDPR's "right to erasure" (Article 17) directly opposes blockchain's immutability. By design, blockchain records are permanent and cannot be altered or deleted without undermining the ledger's integrity. This creates a major issue when individuals request their data to be erased, as fulfilling such requests is technically impossible. The European Data Protection Board has emphasized:
"Technical impossibility is not an excuse for non-compliance" [2].
Even seemingly minor data points, like public keys or timestamps, can lead to complications. If these elements can be linked to an individual, they are classified as pseudonymous personal data under GDPR [2]. For instance, MD5 hashing has been criticized as "trivially reversible" [3], further highlighting the risks. Failure to comply with these regulations can result in severe penalties.
Determining Data Controllers in Decentralized Networks
Blockchain's decentralized structure makes it difficult to assign responsibility for data processing. Under GDPR, there must be a clear "data controller" - an entity that decides how and why personal data is processed. However, in blockchain networks, this responsibility is shared among developers, miners, validators, node operators, and even users. This lack of a central authority complicates compliance.
To address this, the European Data Protection Board suggests using a "factual influence" test to identify roles [2]. For example, while nodes that merely relay transactions might not qualify as controllers, validators who influence transaction prioritization or protocol updates could be considered as such. France's CNIL has also clarified:
"Users who interact with blockchain ledgers for professional or commercial purposes can be classified as data controllers" [5].
This distributed accountability could lead to joint controllership under GDPR Article 26, requiring complex legal agreements. As Maria Okonkwo from GDPRScoreCheck points out:
"Public blockchains storing personal data directly are very difficult to reconcile with GDPR" [3].
Data Retention Limits vs. Permanent Storage
The GDPR's storage limitation principle mandates that personal data should only be retained for as long as necessary for its original purpose. Blockchain, however, inherently retains data indefinitely, making compliance with this principle a challenge [2].
Even technical solutions like cryptographic erasure - where decryption keys are deleted to render encrypted on-chain data unreadable - leave the encrypted data permanently stored on the ledger. The European Data Protection Board's April 2025 guidelines caution:
"Storing personal data on-chain is inherently risky... controllers should avoid putting personal data on the blockchain unless strictly necessary" [2].
Summary of GDPR Conflicts and Possible Mitigations
| GDPR Requirement | Blockchain Conflict | Technical Mitigation |
|---|---|---|
| Storage Limitation | Data stored permanently by design | Off-chain storage with on-chain pointers |
| Right to Erasure | Records cannot be deleted from the ledger | Cryptographic erasure (key destruction) |
| Data Minimization | All transaction data replicated across nodes | Zero-knowledge proofs (ZKPs) |
| Accuracy/Rectification | Historical records cannot be modified | Appending a corrective transaction |
How to Achieve GDPR Compliance in Blockchain
One of the challenges with blockchain technology is its permanent nature, which can clash with GDPR's requirements. The European Data Protection Board (EDPB) emphasizes that "the choice of technology (blockchain) does not justify lowering GDPR standards – controllers are expected to adapt the blockchain's use or design to the law, rather than the other way around" [2]. In other words, businesses must adjust their blockchain systems to align with GDPR, not the reverse.
Building Privacy into Blockchain Design
Privacy should be part of the blockchain's foundation. A key approach is data minimization - avoiding the storage of direct personal data on the blockchain. Instead, use pseudonymous identifiers in smart contracts to limit risks of exposing sensitive information.
When pseudonymization is needed, salted hashes with secret salts or keys can be used. If the salt is deleted, the hash becomes nearly impossible to link back to an individual. The EDPB warns that unsalted hashes, like MD5, are not secure enough since they can be vulnerable to brute-force and dictionary attacks [2][3].
Additionally, permissioned blockchains are often preferred over public ones. They provide clearer accountability and make it easier to identify data controllers. Before launching a blockchain solution, conducting a Data Protection Impact Assessment is crucial. The EDPB advises: "If a blockchain's 'strong integrity' feature (immutability) conflicts with data protection needs, controllers should consider using other tools or technologies altogether" [2].
Another critical step is managing personal data storage off-chain.
Storing Personal Data Off-Chain
To meet GDPR requirements, blockchain systems often store personally identifiable information (PII) in a mutable off-chain database, while only recording a cryptographic hash or pointer on-chain. When someone exercises their right to be forgotten, the off-chain record can be deleted, leaving the on-chain hash as a disconnected string with no reference [6][4].
For enhanced compliance, encrypted data can be stored on-chain, while the decryption keys are kept off-chain. This allows for cryptographic erasure - destroying the decryption key effectively renders the data unreadable. As noted, "By storing data in an encrypted format onchain and maintaining the keys in a mutable offchain environment, an institution can 'delete' the data by permanently destroying the corresponding key" [4].
Organizations also need to prepare for future challenges, such as the potential obsolescence of cryptographic algorithms. With blockchain's permanence, strategies to upgrade encryption or migrate data will be vital as technologies like quantum computing evolve [2].
Privacy-Enhancing Technologies for Compliance
In addition to privacy-by-design and off-chain storage, advanced tools like zero-knowledge proofs (ZKPs) can help blockchain systems align with GDPR. ZKPs allow users to prove facts - such as their age or residency - without revealing personal data, adhering to GDPR's data minimization principle [4][2].
Trusted Execution Environments (TEEs) offer another layer of protection. These hardware-based secure enclaves process sensitive data in isolation, ensuring that even node operators cannot access it. Similarly, zkTLS technology enables smart contracts to verify data from secure, password-protected sources without transferring or decrypting the data on-chain.
For example, in February 2026, Aave Horizon adopted the Chainlink Automated Compliance Engine (ACE) to manage compliance for tokenized assets. The ACE uses privacy-preserving proofs to ensure participants meet regulatory requirements while protecting sensitive data. This approach also aligns with other regulations like MiFID II, avoiding the creation of vulnerable data repositories [4]. This policy-as-code trend is becoming increasingly popular, embedding compliance rules directly into smart contracts.
| Technical Approach | How It Works | GDPR Benefit |
|---|---|---|
| Off-chain storage | Stores PII off-chain; only hashes on-chain | Allows data deletion while maintaining integrity |
| Cryptographic erasure | Encrypted data on-chain; keys off-chain | Enables erasure by destroying keys |
| Zero-knowledge proofs | Verifies information without revealing personal data | Supports data minimization (Article 5) |
| Trusted Execution Environments | Secure enclaves for isolated data processing | Prevents unauthorized access to sensitive data |
Blockchain Types and GDPR Compatibility
When it comes to GDPR compliance, not all blockchains are on equal footing. The type of blockchain - whether public, private, or hybrid - plays a major role in determining how well it aligns with European data protection laws. Here's a closer look at how these blockchain architectures measure up to GDPR requirements.
Public Blockchains and Compliance Challenges
Public blockchains, like Bitcoin and Ethereum, pose some of the toughest challenges for GDPR compliance. The main issue lies in the lack of an identifiable controller and the immutability of the blockchain, which makes it nearly impossible to honor data subject rights like the right to erasure. Even pseudonymous data, such as public keys, can be re-identified through techniques like pattern analysis or linking to exchanges that follow Know Your Customer (KYC) protocols. Maria Okonkwo from GDPRScoreCheck highlights this concern:
"Deploying EU personal data on a public blockchain without an identifiable controller is extremely high risk - there's effectively no way to comply with data subject rights" [3].
Additionally, the global replication of data across nodes creates another major hurdle, particularly when it comes to adhering to EU/EEA restrictions on international data transfers.
Private and Permissioned Blockchains
Private and permissioned blockchains offer a more controlled setup that addresses many of the issues seen in public blockchains. In these systems, participants are identifiable, making it easier to assign GDPR roles like controllers and processors. Prokopiev Law notes that the EDPB strongly advises organizations to use permissioned blockchains for handling personal data, stating:
"Organizations favor permissioned blockchains for personal data use, given that a central managing party can enforce compliance" [2].
Networks like Hyperledger Fabric are examples of permissioned systems that allow for governance structures, such as consortiums, to act as identifiable controllers. These structures can limit node access, ensure confidentiality, and adhere to data minimization principles. Moreover, they allow for administrative intervention, making it possible to fulfill requests like data erasure. Hybrid systems take this one step further by combining on-chain and off-chain data management for even greater flexibility.
Hybrid Blockchain Systems
Hybrid blockchains strike a balance by keeping personal data off-chain while maintaining the integrity of the blockchain itself [3]. In such systems, personal data is stored in a traditional off-chain database, where it can be modified or deleted as needed. Meanwhile, the blockchain only contains cryptographically secure pseudonyms, hashes, or encrypted references to the off-chain data.
When a data subject exercises their right to erasure, the off-chain data is deleted, leaving behind an on-chain hash that no longer has any identifiable link. As Maria Okonkwo explains:
"The key is keeping personal data off-chain and using on-chain storage only for data that is genuinely anonymised or not personal data" [3].
This setup allows organizations to maintain the blockchain's reliability and auditability while ensuring GDPR compliance, including the ability to honor erasure requests.
| Blockchain Type | GDPR Compatibility | Controller Identification | Data Erasure |
|---|---|---|---|
| Public (Permissionless) | Very Low | No identifiable controller; high risk | Technically impossible |
| Private (Permissioned) | High | Identifiable parties act as controllers | Possible via administrative design |
| Hybrid (Off-chain/On-chain) | High (Recommended) | Controller manages off-chain data | Achieved by deleting off-chain records |
Step-by-Step Guide to Blockchain GDPR Compliance
Navigating GDPR compliance for blockchain technology demands a structured approach, starting from the design phase and continuing through regular operations. The European Data Protection Board has made it clear:
"Blockchain technology is not exempt from GDPR requirements, regardless of its decentralized nature or technical limitations" [1].
Here’s how to approach the compliance process effectively.
Conducting a Data Protection Impact Assessment
A Data Protection Impact Assessment (DPIA) is a mandatory step under Article 35 of the GDPR when personal data is involved in blockchain implementations. This assessment must be conducted before any processing begins. The DPIA helps determine whether blockchain is the right choice for your specific use case - sometimes, a traditional database might be a better fit from a compliance perspective.
The DPIA should address several critical factors, including how to handle the challenges of immutability, assess pseudonymization techniques, and manage cross-border data transfers [1]. For decentralized networks, it’s also essential to establish a Joint Controller Agreement that clearly defines the roles and responsibilities of participants, such as node operators and smart contract deployers.
Organizations need to evaluate whether blockchain technology is necessary and proportionate for their goals. Before deployment, they should establish a central legal entity or consortium agreement to act as the primary data controller. Regular audits are equally important, as changes to the network or protocol upgrades can affect the DPIA findings and overall compliance.
Once the DPIA is complete, formalize roles and responsibilities to ensure accountability across the network.
Defining Roles and Responsibilities
In decentralized systems, assigning clear accountability is crucial. As noted earlier, participants such as validating nodes or smart contract deployers may qualify as joint controllers under Article 26 of the GDPR. This classification requires a formal Joint Controller Agreement that outlines the specific legal and technical responsibilities of each party.
To streamline compliance, establish a central legal entity to act as the primary controller and main point of contact for data subjects [4]. As Chainlink highlights:
"Professional participants in a network, such as validating nodes or smart contract deployers, can be classified as joint controllers under Article 26" [4].
Your governance framework should also address data residency rules, ensuring that sensitive metadata is only shared among authorized nodes operating in compliant jurisdictions.
Once roles are defined, continuous monitoring becomes key to staying ahead of regulatory changes and emerging risks.
Continuous Monitoring and Audits
Maintaining compliance requires ongoing monitoring, as both technology and regulations continue to evolve. For instance, the European Data Protection Board released draft guidelines on blockchain compliance on April 14, 2025 [1], illustrating the ever-changing regulatory landscape.
To stay compliant, implement encryption protocols that protect data during cross-border transfers and maintain a verifiable audit trail for regulatory checks. Smart contracts should be designed to use pseudonymous identifiers rather than storing sensitive personal data, aligning with Article 5’s data minimization principles [3]. As the European Union Blockchain Observatory & Forum aptly noted:
"There is no such thing as a GDPR-compliant blockchain technology. There are only GDPR-compliant use cases and applications" [7].
This reinforces the importance of continuous oversight to ensure your blockchain implementation remains compliant over time.
Conclusion
Bringing together the challenges of blockchain's permanence with GDPR's requirements reveals a clear takeaway: achieving compliance demands both thoughtful technical design and strong governance paired with legal expertise. As the European Data Protection Board emphasized in their Guidelines 02/2025:
"Technical impossibility is not an excuse for non-compliance" [2].
The key lies in keeping personal data off-chain. Instead of storing raw data, use cryptographic hashes, encrypted references, or pseudonymous identifiers to respect individuals' rights. If encrypted data must remain on-chain, cryptographic erasure - removing decryption keys to make the data inaccessible - becomes essential.
Another cornerstone is governance. Decentralized systems must have well-defined structures, whether through Joint Controller Agreements, consortium setups, or a dedicated legal entity. These frameworks ensure accountability and provide a clear contact for data subjects. Private and permissioned blockchains, in particular, simplify compliance by establishing defined roles and responsibilities.
By applying these strategies, businesses can address blockchain's inherent challenges, like immutability and distributed accountability, while still enjoying its strengths - transparency, security, and the ability to audit.
However, compliance isn’t a one-time task. It requires ongoing effort. Regular audits, encryption reviews, and staying on top of regulatory changes are crucial as technology and laws evolve. The takeaway is straightforward: build your blockchain systems to meet legal standards, and remain proactive in adapting to future developments.
FAQs
Can a blockchain ever be truly GDPR-compliant?
Blockchain's immutability presents a direct conflict with the General Data Protection Regulation (GDPR), particularly regarding the "right to erasure" outlined in Article 17. This regulation allows individuals to request the deletion of their personal data, but blockchain's unchangeable nature makes such deletions impossible without undermining the integrity of the ledger.
To navigate this issue, many organizations opt to store personal data off-chain, using the blockchain only for encrypted references or pointers to that data. While this approach reduces some risks and aligns more closely with GDPR requirements, it doesn't completely resolve the underlying tension between blockchain's design and GDPR's demands. This makes thoughtful system design and robust safeguards essential.
Who is the GDPR data controller in a decentralized blockchain?
In decentralized blockchains, figuring out who qualifies as the GDPR data controller can be tricky. For permissioned blockchains, the responsibility often falls on the entity or consortium overseeing the network. However, in permissionless blockchains, it's less clear. Developers, participating nodes, or validators could potentially act as controllers, but there's no definitive answer. The absence of a central authority adds to the challenge of assigning compliance duties.
What’s the safest way to handle the GDPR right to be forgotten on blockchain?
To navigate the tension between blockchain's immutability and GDPR's requirements, it's best to adopt privacy-by-design principles. Here’s how:
- Avoid storing personal data on-chain: Instead, keep sensitive information off-chain and rely on cryptographic references like hashes to link the data.
- Use encryption with destroyable keys: Encrypt data and ensure the keys can be destroyed if requested. Once the keys are gone, the data becomes inaccessible.
- Consider private or permissioned blockchains: These systems provide greater control, making them a popular choice for meeting GDPR compliance needs.
This approach helps maintain blockchain's integrity while respecting data privacy laws.